The $1.6 Million Weekend: Why Simple API Gateways Fail in the Agentic Age
The business is building an AI-enabled contract review API that costs $1.58 per document to process: upload the contract, run five quotes through LLM, flag risks, and generate a summary. The economic unit makes sense, and the API works well when called from internal applications. Then the team exposes this API through MCP for use, making it an agent API.
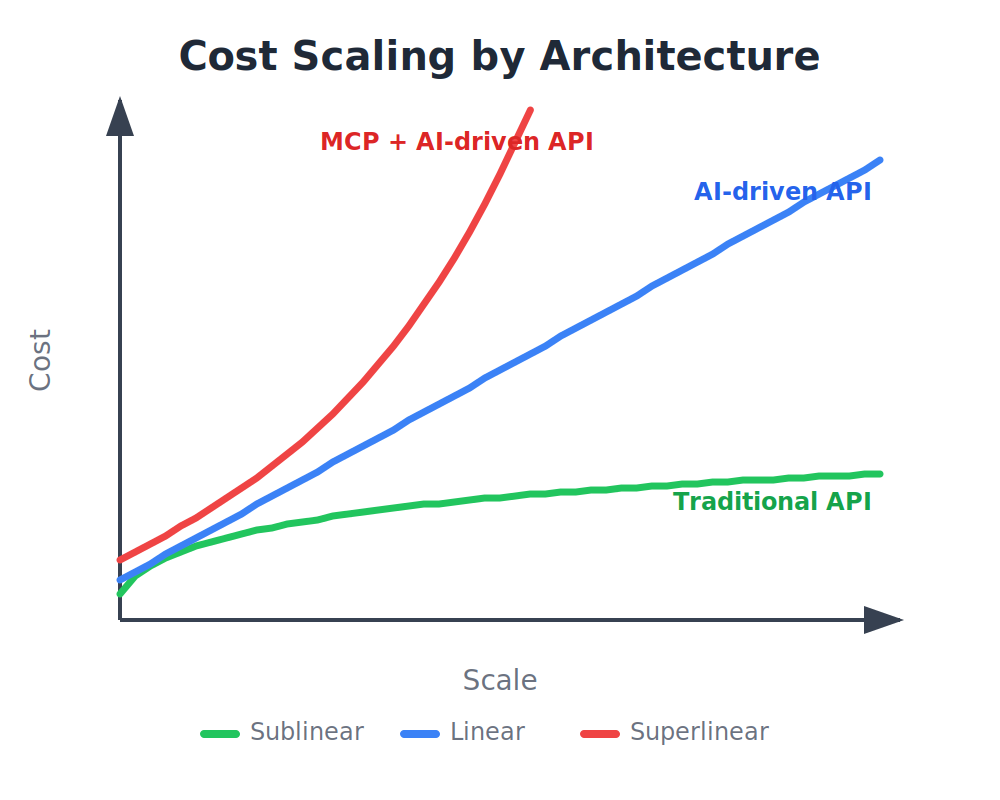
On Friday evening, the agent hits the deadline and starts trying again. By Monday morning, that one post had been viewed a thousand times. Multiply that by a collection of 1,000 contracts, and the bill for the weekend comes to $1.6 million. Traditional APIs have had strong economics due to lower-than-linear cost curves. Cost curves for AI-driven APIs are steep and linear due to the token economy, but they are manageable. When an AI API is exposed through an MCP for use, costs can spiral out of control when agents behave in unpredictable ways.
Through the lens of the standard API gateway, each request is successfully authenticated. The token was valid, the level limits were respected, and the scope was approved. The gateway approved each one because it checked the requests individually, with no way to tell if request #847 was the same as request #846 that preceded it. This presents a fundamental problem: non-root API gateways are not equipped for agent-based use. The architectural assumptions that have served the API management industry for decades are falling apart when non-deterministic agents become API consumers.
Blind Agent Problem in Agentic APIs
The AI gateway cannot detect the intent or reasoning of the LLM. It can only see the usage of the token, the instrument being called, and the parameters being passed. It cannot tell whether the current request is the 500th retry of a failed operation, or whether the agent is drifting from searching for documents to sending the administrator’s database. Each request appears valid, but the pattern remains invisible, which is why the gateway acts as a blind proxy.
Enterprise customers are beginning to test whether gateways can track conversational context as they meet the limitations of unstructured architectures in production. Most MCP gateway implementations today focus on MCP security and individual application visibility. They use the MCP-Session-Id for routing such as ensuring that requests arrive at the same backend, but not for handling behavior such as loop detection or tracking of collected funds. The session identifier is present, but the session information intelligence is not.
APIs used by humans have never had this problem. These API users are accountable (with API keys), their behavior is predictable (following the same code paths), and they stop quickly (like after a few retries). Although the input may be different, the code is not rewritten in an instant. The use of the agent does not show any of these features. They create ownership gaps, blurring the line between user responsibility and agent autonomy. They make parameters arbitrary and tricky, meaning that the same input can trigger very different tool calls. Agents try and act tirelessly until a result is achieved.
For traditional APIs, fixing both intentional and unintentional API abuse has always been a whack-a-mole game. However, correcting an MCP injury is like playing whack-a-mole a thousand rounds a minute. The agent changes its behavior faster than you can close the gaps.
“Fixing API abuse is playing Whack-a-Mole…Fixing MCP abuse is playing Whack-a-Mole a thousand rounds a minute.”
The Three Pillars of Agentic API Governance
Autonomous agent APIs require a framework built on three pillars: economics, behavior, and identity. Each works at the application, session, and organization levels. Time-level management is where the most significant challenges arise, as most API gateways limit scalability and performance.
Economic dominance is often where groups start to feel the pain. Recently, AI gateways introduced a token level limit as AI API requests can have very different LLM cost profiles. However, the token level limit drops when the use of an agent is introduced. The token rate limit measures output, not waste; a slow retry loop exceeds all rate limits while burning money for hours. Thus, static limits will evolve to session-based tracking locked to MCP-Session-Id: cumulative costs, spend speed monitoring that flags abnormal burn rates, loop detection, and hard caps that trigger a kill switch when limits are exceeded. When the agent sent 127 similar requests and consumed $200 at $3.21 per minute, that pattern is a smart move to avoid the $1.6 million problem initially shared.
Ethical governance regulates what agents are allowed to do and catches mistakes that people would not make since agents do not respect boundaries. If an agent with a read: data range tries to call DELETE/users/all, the gateway should recognize that the range is not equal and block the request. While the best practice was a well-refined API, this is now essential for agent use.
Hidden issues require session context to detect. An agent who starts by searching documents, moves on to HR records, and requests a database submission may send individual valid calls with appropriate scopes, but the sequence reveals an escalation of privilege. Detecting scope drift, scoring risk, and triggering human-in-the-loop approvals all require follow-up behavior at all times.
Ownership management presents the most difficult recovery challenge. What happens if the agent needs to use the newly discovered API? Traditional OAuth was not designed for independent agents as it takes human registration requests through the developer portal to obtain credentials. Agents need to move at machine speed. The MCP 2025 specification addresses this with Client ID Metadata Documents (CIMD), which allow agents to capture their identity, allowing agents to securely self-register without a human-provided workflow. By adopting CIMD, agents can register in milliseconds, moving at the speed of LLM rather than the speed of the developer portal.
Accountability is equally important. If a user spawns 1,000 agents, with each spawning of multiple agents, you need to know both who the user is and which agent is running so that the audit logs can identify which agent deleted the records at 3 AM. Tokens must capture and verify both user and agent identities so that audit and compliance reporting mechanisms accurately reflect actions.
AI Gateway Becomes Session-Aware
Using this framework requires a hybrid architecture. Identity verification should remain stateless, handling JWT signatures, claim issuance, and CIMD verification to enable horizontal scaling. Management, however, evolves into status, tracking money, aggregate statistics, and behavioral patterns in the cache identified by the MCP-Session-Id. This session state turns the blind agent into a smart governor of your agent APIs, able to detect loops, scope drift, and escalation patterns that per-request authentication would never detect. A temporary cache (like Redis or Memcached) allows session-aware tracking with sub-millisecond overhead. This will require a rethinking of enterprise architecture and middleware. Over the past 20 years, enterprise architecture has settled on stateless RESTful APIs, with statehood often seen as the enemy of scale. Agent use is now bucking those trends.
Gartner predicts that more than 40% of agent AI projects will be canceled by 2027, mainly due to rising costs and inadequate risk management. Companies today face competing mandates: they must deploy MCP capabilities quickly to stay competitive while also controlling agent usage before it causes damage to the entire business. Many organizations prioritize speed and think they can regain control over time.
That approach presents great dangers. A $1.6 million weekend isn’t a marginal issue to be solved over and over again; it is a predictable consequence of applying informal governance to important problems. Teams that recognize this early will build a robust management infrastructure from scratch, designed for agent use. Those who do not learn it will learn the same lesson at a much greater cost.